Did you know…
These are just some of the systems our contributors have lived through. Now in Norway, they’ll tell how digital repression works—and why it’s spreading.
What is digital repression?
Digital repression refers to the use of digital information and communication technologies to surveil, manipulate, or coerce individuals or groups in order to control public debate. It is a major issue in a wider discussion about human right and repression.
Across countries, the methods typically cluster into four areas:
- censorship
- misinformation/disinformation
- mass surveillance
- invasive spyware.
These practices are used by authoritarian regimes and, increasingly, by backsliding democracies—at home and against diaspora communities abroad.
The landscape is evolving. Governments are moving from broad shutdowns to more targeted, harder-to-see blocking, expanding camera networks and AI-driven identification, and experimenting with deepfakes to harass critics. Mitigation discussed in the same assessment includes stronger international norms and rights-preserving design by platforms and vendors.
At the same time, citizens and activists continue to adapt—using VPNs, Tor, mesh networking, wordplay, and even mirrored/upside-down media to bypass automated filters—often only temporarily. Our project documents both the controls and these workarounds through first-hand accounts.
Project proposal
Digital Repression is a planned 2026 anthology that will collect first-hand accounts from writers, activists, and journalists now living in exile in Norway who have experienced digital repression across the world. Told in their own voices, these stories will show how firewalls, internet shutdowns, state-approved “secure” apps, Super Apps, CBDCs, cloud seizures, coerced platform compliance, and cameras + AI are used to control speech—and what that costs in real lives.
The book will chart the rise of these systems over the past decade and trace their future trajectory: how they spread across borders, how fast they evolve, and where they may surface next—even in open democracies. Each chapter pairs a personal testimony with a short, plain-language explainer of the tool involved, plus a timeline marker that situates the event within global trends.
Why Norway—and why this book now?
Norway’s long-standing commitment to human rights and freedom of expression includes providing a safe haven for people who have faced digital repression elsewhere. Publishing this anthology here lets us learn directly from those now living in Norway whose experiences show how these controls work in practice—and how aspects of them can follow people across borders.
Digital repression is evolving quickly and is not limited to state actors. Platform policies, data brokers, commercial spyware, payment rails, and cloud infrastructure all shape what can be seen, said, financed, or preserved. This book serves as a field guide to that landscape: first-hand cases paired with plain-language explainers that help readers and policymakers recognise emerging patterns, assess proportional responses, and contribute to Norway’s wider, principled engagement on human rights as these tools spread.
Digital Repression Globally
The map below situates the project’s themes worldwide. The highlighted countries offer examples of current practices and trends, underscoring that these issues are international in reach and impact.
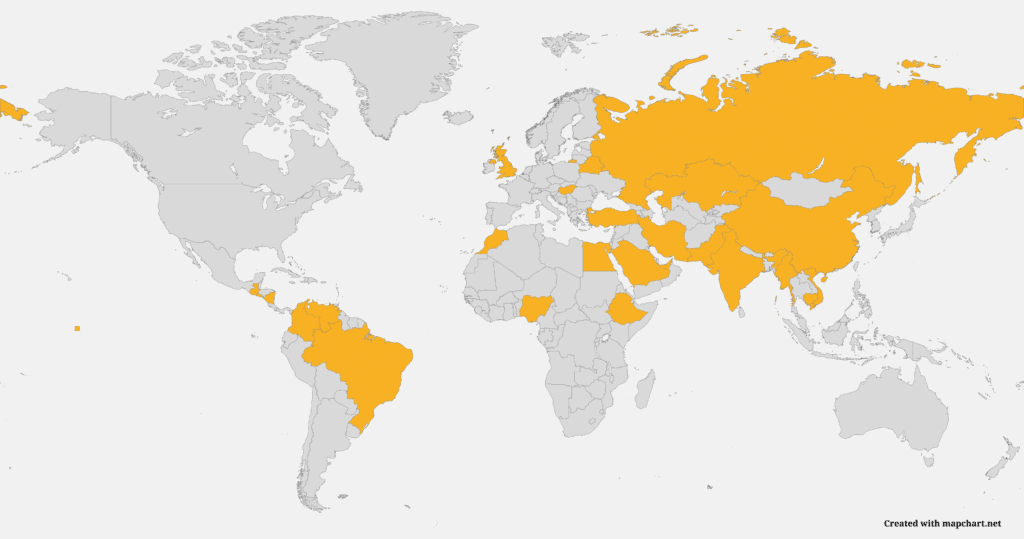
Iran — National firewall; protest shutdowns; state-approved VPNs; platform blocks; AI + cameras to enforce hijab; arrests via phone searches; cloud seizures.
Russia — “Sovereign internet”; SORM interception; platform blocking; throttling during protests; pressure on platforms; domestic app/payment stack.
Egypt — Broad website blocking; arrests over social posts; anti-terror cyber laws; targeted spyware; intermittent throttling/shutdowns.
China — Great Firewall; Super App ecosystem (WeChat); mass CCTV + facial recognition; data localisation; real-time content filtering; CBDC (e-CNY) pilots.
Turkey — Forced platform reps & fast takedowns; DNS/IP blocking; throttling after crises; prosecutions over tweets; data-localisation pressure.
India — World-leading regional shutdowns; strict takedown rules; platform liability; SIM/ID linkages; chilling effect on journalists/NGOs.
…and many more
Pakistan — PTA blocking (YouTube/TikTok episodes); cybercrime law used against critics; election-period throttling/shutdowns.
Bangladesh — Digital Security Act arrests; news site blocks; protest-period throttling; surveillance of opposition.
Myanmar — Post-coup blackouts; mass arrests via device searches; mandatory SIM registration; platform bans.
Saudi Arabia — Prosecutions based on tweets; targeted spyware; cybercrime laws; coercion on platforms for takedowns.
UAE — Extensive surveillance; restrictive cyber laws; VoIP blocks; platform pressure; arrests for online speech.
Belarus — Nationwide throttling/shutdowns during protests; DPI filtering; data-driven arrests; Telegram targeting.
Vietnam — “Force 47” cyber unit; data localisation; forced platform removals; arrests for Facebook posts.
Cambodia — National Internet Gateway for centralised filtering; arrests for online dissent; pressure on ISPs.
Ethiopia — Regional shutdowns (elections/conflict); blocking of platforms; harassment of online media.
Nigeria — Twitter ban (2021) precedent; social media bill attempts; SIM-ID linkage; CBDC (eNaira) privacy concerns.
Kazakhstan — HTTPS interception certificate episodes; protest-time shutdowns; targeted blocking.
Hungary — Spyware (Pegasus) reports on journalists; media capture; chilling effects on sources.
Morocco — Pegasus surveillance cases; prosecutions based on digital evidence; pressure on independent media.
United Kingdom — Online Safety Act risks to encryption & over-removal; bulk powers debates; potential model others could copy.
Getting involved
We will issue a public call in late autumn 2025 for first-hand accounts from writers, journalists, and activists now living in Norway who have experienced digital repression anywhere in the world. If this is you, please get in touch now and we’ll ensure you are included when the call opens.
Who we’re looking for
People with lived experience of measures such as:
- National firewalls, blocking/throttling, and internet shutdowns
- Random device searches, data extraction/forensics; device/location history used in prosecutions
- Government-backed hacking/spyware, phishing, SIM-swap or account takeovers
- State-approved “secure” apps (incl. VPNs) or app-based surveillance that routes/monitors traffic
- Cloud account access, seizure, or deletion; compelled password disclosure; loss of archives
- Platform pressure: takedowns, account suspensions, geo-blocking, data-localisation compliance
- Bot-driven mass reporting, coordinated harassment/brigading, gendered abuse, doxxing
- Super apps linking messaging, payments, ID and mobility; movement or network mapping
- CBDCs/financial controls, payment freezes or donor tracing; bank/platform restrictions
- Cameras + AI (face/plate/gait recognition), e.g., dress-code enforcement and crowd identification
- Cross-border intimidation of diaspora and families; threats tied to online activity
- Cryptocurrency as constraint (e.g., mining strains) or as a factor in prosecutions
We also welcome accounts of how people navigated or mitigated these controls, including:
- Customised VPN setups; Tor and bridge-based access; traffic obfuscation approaches
- Mesh/off-grid networking via Bluetooth or Wi-Fi; opportunistic relays; offline “sneakernet” exchange
- Linguistic strategies (wordplay, coded phrasing, homographs, zero-width characters) to avoid automated filters
- Visual workarounds (text-in-image, reversing/mirroring or subtly altering images to pass OCR/vision filters)
- Content mirroring and diaspora relays; staggered/time-zone posting; alternative domains
- Operational hygiene such as metadata minimisation, safer backups, or compartmentation of accounts/devices
(Planned support includes an honorarium, editorial guidance, and translation where needed. All enquiries are handled confidentially.)